by Harshala | Dec 28, 2018 | Content Management Systems, Content Strategy, Industry News, Web Content, Web Design, Web Development
What is a static website generator?
A static site is a collection of pages contained in basic HTML files. A static site generator is a compromise between using a hand-coded static site and a full CMS. You generate an HTML-only website using raw data such as Markdown files and templates. The resulting build is transferred to your live web server.
An Introduction to Static Site Generators article was published a few years ago. The basic concept has remained constant. It explains the popularity of static site generator. It also help people of all skill levels understand exactly what static site generators are, acknowledge their advantages, and understand if their limitations are a deal-breaker or if, on the contrary, they can be overcome.
How static sites work?
The proposition of a static site is to shift the heavy load from the moment visitor’s request the content to the moment content actually changes. Using a news kiosk metaphor, think of a scenario where it’s the news agencies who call the kiosk whenever something newsworthy happens.

(more…)
by Will Ellis | Dec 14, 2018 | Content Strategy, Cyber Crime, ECommerce, Industry News
If you earn a living – or even just spending money – selling stuff online as an affiliate, you should be concerned about cookies.
Digital cookies are the behind-the-scenes gizmo that credits you with a sale generated by a web page visitor. What you may not realize is that it is entirely possible for a clever hacker to hijack those cookies and end up with a sale that should have been credited to your account.
We’re talking big money. Shawn Hogan drew the attention of the FBI when he redirected around $28 million from rightful affiliates to his own account over the course of a few years.
The process in question is known as cookie hijacking or session hijacking.
To protect your cookies, it’s time to get serious about cybersecurity. It’s time to learn what cookies are, how they get hijacked, and what you can do minimize the risk.
Understanding Cookies
A cookie is a small packet of data that a web server transfers to a browser when someone visits a web page. Think of it as a message that originates with the server and is received by the visitor. Unless the visitor has blocked cookies, that data downloads onto the system and makes it easier for the page to load the next time the visitor returns.
That’s the main purpose of cookies: to make visiting a page simpler by ensuring it loads a little faster. It also helps the owner of the page have a better idea of how many visitors the page generates, if there are return visitors, and in general keep up with traffic patterns.
As it relates to affiliates, those cookies also make it easier for you to get credit when a consumer purchases something via your page.
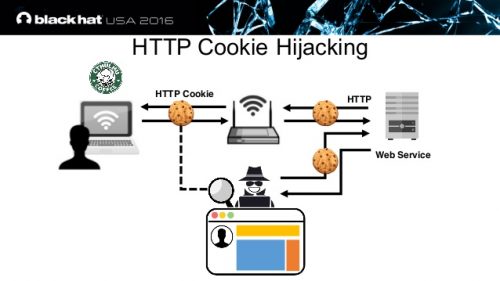
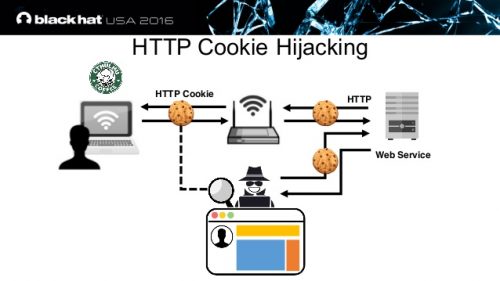
How Can They Be Hijacked?
Cookies are dead simple, which may be why they are often overlooked as a means of committing a crime. All it really takes is for a hacker to seize the cookie and make a minor alteration.
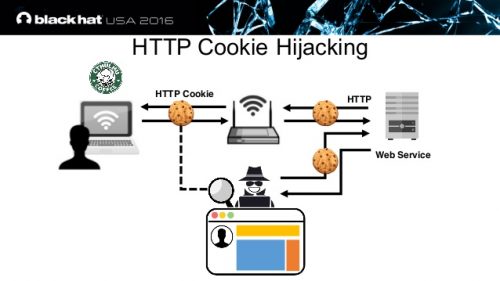
The next time a visitor lands on your page the cookie ensures that the hacker’s content loads. In most cases, it will be an almost perfect mirror of the original page. What’s different is the packet of information downloaded for the session is not original. It’s been altered. That sets the stage for the hacker to control what happens next.
What Does this Mean For Affiliates?
Why would cookie hijacking matter to an affiliate? After all, doesn’t the visitor use the URL to get to the right place and make a sale? What does the cookie have to do with it anyway?
The thing to remember is that the cookies make loading the order page easier. If you alter the data in the cookie so that the affiliate ID is no longer the same, the credit for that order is redirected to another source. That’s because the cookie is often stored in the raw URL for the session. Alter the cookie by changing the affiliate ID and the end user doesn’t really notice anything.
In other words, it appears that the consumer is placing the order with you, but it’s actually being placed with someone different. You never get credit for the sale and certainly don’t receive a commission. That makes this little malfeasance a form of affiliate fraud.
How Do You Know If Your Affiliate Cookies are Hijacked?
Cookie hijacking is difficult to spot. In fact, it would be almost impossible to detect when it happens during a live session. Whether the session hijacking is active or passive, you only have a chance of identifying the damage once it’s done.
One sign that something is not right has to do with the performance of the web page. If it begins to function erratically for no apparent reason, that could mean something has been altered. Alternatively, the page shutting down can be an indication something has been changed. At this juncture, you may want to check the cookies related to the page closely and see if the affiliate ID or even some other aspect of the cookie code is not as it should be.
If your affiliate partner emails or texts you when individual sales occur, compare that information to the commission report. If they don’t match, and there’s no evidence of returns or canceled orders, someone else is ending up with your commissions.
Are There Ways to Prevent Hijacks?
Preventing a hijack is actually simpler on the visitor side. If the page visitor has up to date malware and antivirus software, the protections in those programs will likely spot that something was changed during a session. This gives the individual the opportunity to end the session before completing a transaction. The problem is the high rate of old malware and antivirus software in use.
Your affiliate can provide some support in terms of preventing cookie-jacking. Depending on how the servers download cookies and what sort of security is used for your customized affiliate page, it may be possible to prevent hacking software from modifying the cookies and the session ID that’s generated.
Create Your Own Encrypted Internet Connection
It’s not as complicated as it sounds. The concept of a virtual private network or VPN is coming into its own and likely will become an indispensable component of internet connections before too much more time has passed.
A VPN works in conjunction with your ISP. It is a separate service that encrypts the data that flows between your device and the internet. You don’t have to be a cryptographer to realize that encryption makes it harder for a hacker to complete his task. The extra ten or so bucks a month is money well-spent.
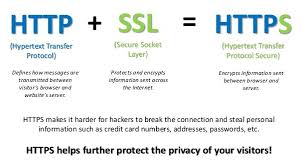
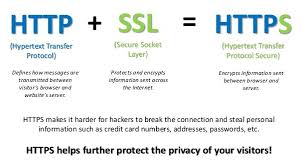
Make sure your affiliate pages use HyperText Transfer Protocol Secure (HTTPS) rather than HyperText Transfer Protocol (HTTP). Doing so adds another layer of protection by scrambling the code that’s shared between the originating server and the recipient
The Bottom Line
You don’t devote time and energy to building a business only to have someone else steal sales as certainly as if they reached over and grabbed twenty bucks from your wallet. Make it a point to educate yourself about online security. Subscribe to a blog or two. You don’t have to be a techie to stay updated on the latest threats and keep solid malware protection in place.

by Harshala | Dec 7, 2018 | Content Management Systems, Industry News, State of the Web, Web Development
PHP Matters
PHP is a commonly used language for web sites and web application development. It is a general purpose, server-side scripting language run a web server that’s designed to make dynamic pages and applications. PHP is mainly focused on server-side scripting tasks, such as collecting form data, generating dynamic page content, or tracking session state. PHP also does much more.

(more…)

by Harshala | Nov 16, 2018 | Industry News, Mobile Web
What is Voice User Interface Design?
A voice-user interface (VUI) makes human interaction with computers possible through a voice/speech platform in order to initiate an automated service or process.” VUI design focuses on the process of interaction design for the user and the voice application system.

(more…)

by Harshala | Nov 9, 2018 | Content Management Systems, Industry News, State of the Web, Web Accessibility
What is WordPress Project Gutenberg?
Gutenberg is more than an editor. While the editor is the focus right now, the project will ultimately impact the entire publishing experience including customization (the next focus area). Gutenberg looks at the editor as more than a content field, revisiting a layout that has been largely unchanged for almost a decade. This allows us to holistically design a modern editing experience and build a foundation for things to come.
Here is the link to get more information on the Gutenberg plugin.

(more…)

by Harshala | Oct 19, 2018 | Industry News
What is Solid?
Solid is an exciting new project led by Prof. Tim Berners-Lee, inventor of the World Wide Web, taking place at MIT. The project aims to radically change the way Web applications work today, resulting in true data ownership as well as improved privacy.
In the article written by Tim Berners-Lee about the Solid Framework, he believes Solid will resonate with the global community of developers, hackers, and internet activists who bristle over corporate and government control of the web. “Developers have always had a certain amount of revolutionary spirit,” he observes. Circumventing government spies or corporate overlords may be the initial lure of Solid, but the bigger draw will be something even more appealing to hackers: freedom. In the centralized web, data is kept in silos–controlled by the companies that build them, like Facebook and Google. In the decentralized web, there are no silos.

(more…)